The Changing Landscape of Operational Technology Security
Understanding the OT Exposure Threat
Historically, many have viewed operational technology (OT) environments as impenetrable fortresses, safely isolated from the public internet. This perception, however, is rapidly becoming outdated. Today, close to 20 million OT devices are online, accessible, and becoming increasingly vulnerable to cyber threats. A collaborative study by Palo Alto Networks, Siemens, and the Idaho National Laboratory highlights a dramatic 332 percent increase—from 6 million devices in 2023 to 20 million in 2024—demonstrating that the OT attack surface has expanded well beyond the protective confines of the plant.
The Scale of Online Exposure
Cortex Xpanse, a tool for identifying vulnerabilities, recorded over 110 million instances of OT devices exposed on the internet in 2024, marking a staggering 138 percent increase from the previous year. This figure includes real-time observations of devices, underscoring just how dynamic the threat landscape is. Notably, Tridium Niagara, primarily used in HVAC and facility management systems, was frequently observed online. Interestingly, this exposure tends to surge during summer months, correlating with seasonal installation and maintenance cycles. Such patterns show that risks often arise from routine operations rather than malicious intent, emphasizing the importance of safeguarding common operational functions.
The 185-Day Warning
To mitigate threats effectively, understanding the timeline of adversarial behavior is crucial. The research indicates that a significant majority—82.8 percent—of cyber adversary activity takes place during a preparatory phase. On average, threat actors may linger for 185 days after their initial observation, analyzing port vulnerabilities and testing authentication pathways. Cortex Xpanse can map this crucial precursor period by continually scanning the public IPv4 space and fingerprinting exposed services. When a management portal appears publicly, defenders have a prime opportunity to respond proactively, even while attackers are still probing.
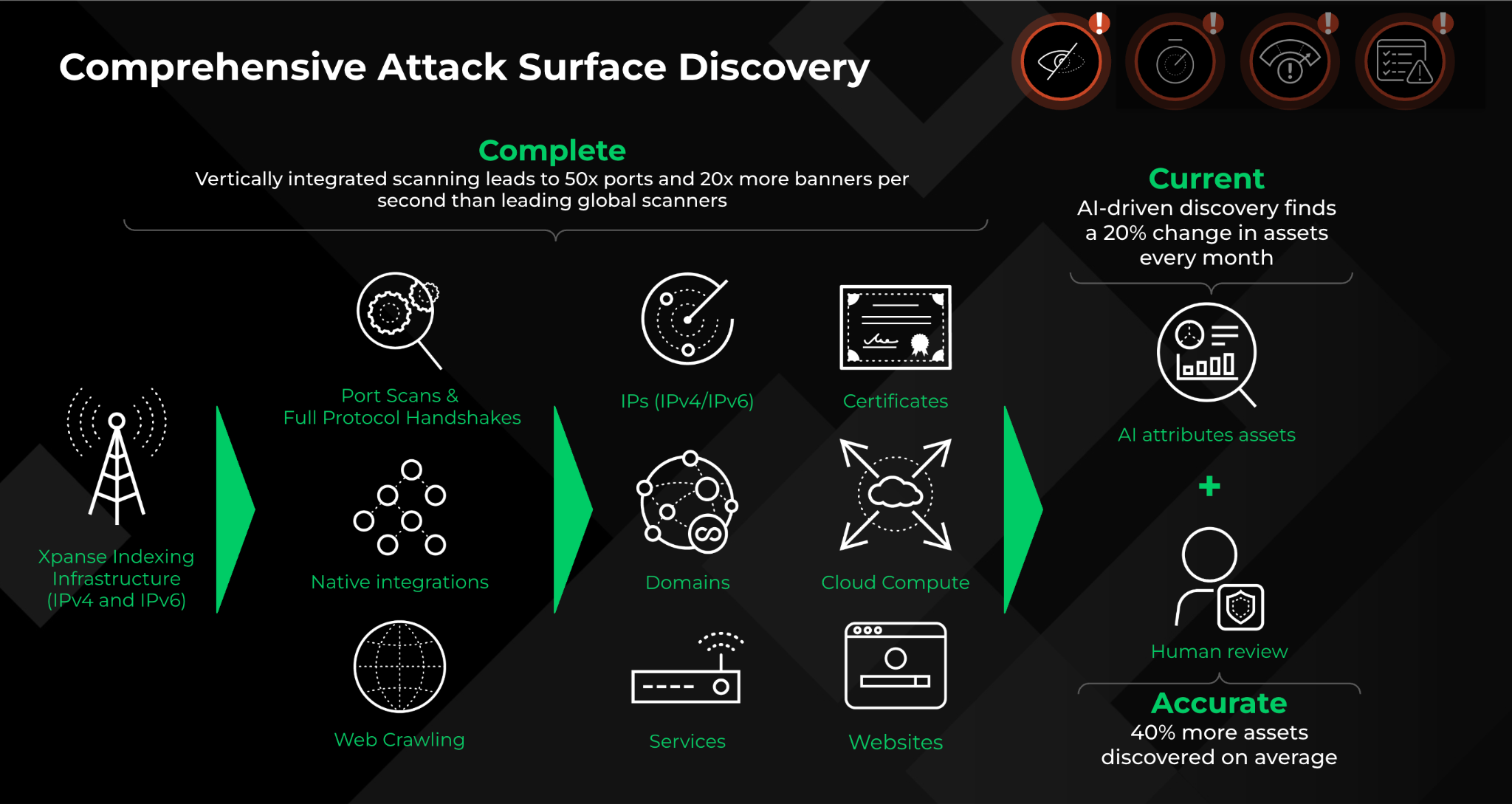
Active Defense Through Enhanced Visibility
Relying on static snapshots of network security is insufficient, particularly given the rapid pace at which these environments evolve. Xpanse provides continuous discovery, effectively distinguishing between intentional exposure and accidental leaks. This dual approach combines two critical perspectives:
- External Exposure: Insights into internet-visible hosts, open ports, services, and applications.
- Internal Context: Information about asset roles and their criticality to business operations.
Together, these perspectives empower security teams to prioritize threats more effectively.
Case Study: Real-World Resilience in Action
The implications of effective OT security monitoring can be profound. Take, for instance, CBTS, a leading technology provider that integrated Cortex Xpanse into its security strategy. During a significant organizational restructuring, the security team utilized Xpanse to meticulously catalog all internet-facing assets, identifying and addressing thousands of accidental exposures in real time. By evolving from a “detect and ticket” methodology to an automated platform approach, they consolidated 20 different tools into one cohesive source of truth. This transformation significantly reduced their median time to resolution from multiple days to just 13 seconds.
From Reactive Response to Strategic Mitigation
Visibility alone won’t resolve backlog challenges. Many organizations categorize every vulnerability as urgent without evaluating existing defenses. For this reason, Cortex Exposure Management streamlines processes by utilizing Security and Compensating Controls. This helps ensure that teams focus on genuine threats while also capturing evidence of mitigation efforts. The benefits of this restructured approach are twofold:
- Optimized Operations: By minimizing false urgency, security teams can concentrate on unaddressed threats.
- Empowered Decision Making: Enhanced clarity around residual risk aids in budget justification and informed risk acceptance.
A New Source of Truth
The days of the hidden industrial network are over. Cortex Xpanse offers a comprehensive landscape view that enhances both security and operational efficiency. As OT converges with IT, this integrative view allows teams to automate workflows, assess residual risk, and take decisive action before adversarial activity can escalate.
Security in modern operational environments demands a rethinking of traditional approaches. For those interested in deepening their knowledge, the Intelligence Driven Active Defense white paper provides valuable insights. Additionally, scheduling a personalized Cortex Xpanse demo can assist teams in closing the critical 185-day response gap.